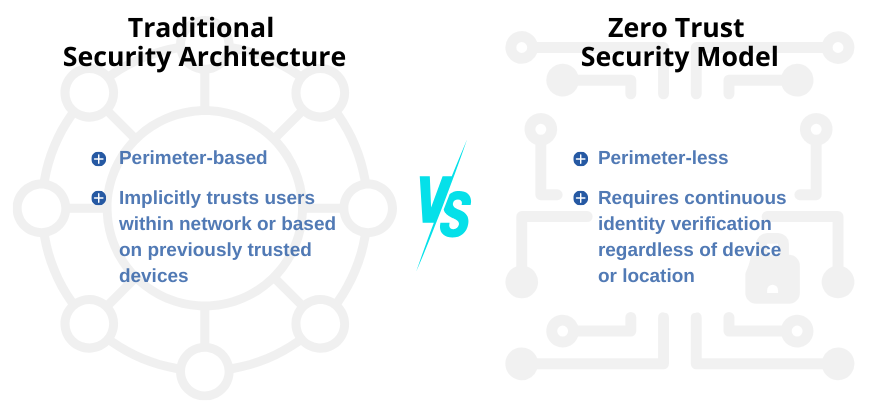
A company’s network is no longer contained within the four walls of the office. Remote and hybrid workforces have enabled a global perimeter that exposes networks to malicious access and activity. Coupled with sophisticated cyber threats that evolve in real-time, traditional security models are proving to be increasingly inadequate in safeguarding sensitive data.
As a result, the concept of a zero trust security architecture has emerged as a progressive and formidable defense strategy. But implementing a zero trust model should be carefully considered for not only its inherent benefits but its ultimate impact on both a business’s security effectiveness and culture.
What is Zero Trust Security?
Companies who implement a zero trust model adopt a “never trust, always verify” approach to security and data protection. Operating under the assumption that no entity or device (whether inside or outside the corporate network) should be trusted by default, the zero trust framework requires continuous authentication and authorization from every user, device, and application that requests access.
Zero Trust Network Access (ZTNA) Benefits
Zero trust network access (ZTNA) is a proactive, adaptive, and robust security model that empowers organizations across all industries to maintain the confidentiality, integrity, and availability of their critical data as they navigate an increasingly sophisticated threat landscape. Following are some of the key benefits of zero trust security:
- Minimize Your Attack Surface: With less traffic inherently authorized to access your network, you can limit your overall attack surface, giving hackers less opportunity to penetrate your network and compromise your data.
- Boost Your Threat Protection: Real-time monitoring, advanced encryption and permission restrictions allow you to rapidly detect and contain threats.
- Increase Visibility and Control: Get complete visibility into your corporate network traffic and user behavior, and use that knowledge to inform and adapt your internal policies, access levels and security stack over time.
- Improve Regulatory Compliance: Zero trust can help you enable compliance with increasing data privacy regulations from the likes of HIPAA, CCPA, FISMA, and others, that increasingly require advanced authentication and access control mechanisms.
- Enable IT Agility & Digital Transformation: With a perimeter-less approach, zero trust facilitates a hybrid approach to technology, wherein you can seamlessly leverage remote access capabilities as your business scales and evolves — and whether users operate in-office, remotely or while traveling.
Key Considerations for Implementing a Zero Trust Architecture
As you contemplate the advantages of ZTNA — including its impact to your IT budget and how you or your MSP will manage the implementation — be sure to take these additional factors into consideration:
Culture
Zero trust is not a widget or tool you can simply turn on and enable for success. It requires a shift in mindset — from the top of the organization down. Not only may users and administrators need time to adjust to the “new normal” of continuous verification, but additional steps and requirements to verify access and privileges can potentially have an adverse effect on employee morale and productivity if not carefully considered, communicated and rolled out.
Integration
Integrating zero trust principles into existing systems or workflows may pose challenges. Legacy infrastructure or applications may not be inherently compatible or could necessitate additional planning, upgrades or investments to ensure a thorough ZTNA policy is enabled across the organization. Before taking the leap, you may want to perform an inventory of your technology stack to ensure you design an efficient and effective path to implementation.
User Experience
As with most modern data protection safeguards, striking a balance between security and user experience is critical. Adopting a zero trust security framework will require careful consideration of the impact to users. Integrating single-sign-on (SSO) capabilities into the process will help enable a smoother transition, and of course, effective communication and user training will be important tools to limit friction and enable effective adoption with minimal disruption.
Enable Zero Trust Security with Omega Systems
We are fielding questions from customers about ZTNA more and more, which is why we’ve carefully designed a zero trust security stack that helps increase cyber threat protections, enables dynamic permission controls and gives businesses greater confidence against growing security threats. If you’d like to learn more about Omega’s zero trust solutions, please connect with us today.